Posted by: Pdfprep
Post Date: October 14, 2020
A security administrator has found a hash in the environment known to belong to malware. The administrator then finds this file to be in in the preupdate area of the OS, which indicates it was pushed from the central patch system.
File: winx86_adobe_flash_upgrade.exe
Hash: 99ac28bede43ab869b853ba62c4ea243
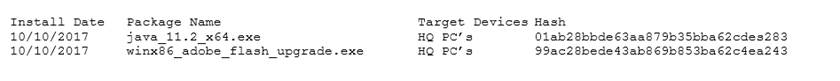
The administrator pulls a report from the patch management system with the following output:
Given the above outputs, which of the following MOST likely happened?
A . The file was corrupted after it left the patch system.
B . The file was infected when the patch manager downloaded it.
C . The file was not approved in the application whitelist system.
D . The file was embedded with a logic bomb to evade detection.
Answer: D

Leave a Reply